John Jay Research Blog
The Office for the Advancement of Research, as part of our Public Scholarship Initiative, actively solicits blog entries from John Jay faculty, staff, and external scholars working on issues of key contemporary and historical significance. We promote these entries on social media, including Facebook and Twitter, as well as within the university through a partnership with our Marketing and Development Office. If you wish to contribute an entry, please contact Research Communications Specialist Remmy Bahati at rbahati@jjay.cuny.edu with a brief (1-2 sentence) summary of your proposed entry.
Honoring the Legacy of Dr. Maureen Allwood

John Jay College staff in the Office for the Advancement of Research join the college community in mourning the passing of Dr. Maureen Allwood, a distinguished researcher, educator, advocate, and friend. Dr. Allwood’s sudden departure on Monday, March 4, in Providence, Rhode Island, has left a profound void in the hearts of those who knew her. Yet, her legacy of warmth, inspiration, and tireless dedication to marginalized communities will endure for generations.
A valued scholar in the field of psychology, Dr. Allwood’s work focused on understanding the developmental effects of trauma and violence, particularly emphasizing their disproportionate impacts on different sociodemographic groups. At John Jay College, she was a beacon of academic excellence and served as a professor of psychology since 2007. She also co-directed the department’s mentorship program for underrepresented and first-generation undergraduate students, leaving an indelible mark on the community with her passion and expertise. Her commitment to fostering diversity, equity, and inclusion within academia was unwavering, and her impact extended far beyond the classroom.
While grieving, her profound impact on the John Jay College community resonates deeply. Reflecting on her legacy, Dr. Angela Crossman, the Interim Dean of Faculty and Professor in the Department of Psychology where Dr. Allwood worked, aptly captured the sentiments of many, stating:
“Dr. Allwood’s passing was an incredible shock that is still difficult to fathom and is a tremendous loss to us all. She was a brilliant scholar, a passionate mentor and teacher, a dedicated and thoughtful colleague, and a warm and kind friend. I admired her greatly, appreciated the important work she was doing on the impact of trauma and violence exposure on youth development, and was always incredibly grateful that she chose to make John Jay her academic home. The world is a better place for her having been a part of it, and she will be deeply missed by her friends, family, colleagues, and students – students who will carry on her legacy of impactful and important scholarship conducted with integrity, rigor, and care.” said Dr. Crossman.
Beyond her scholarly pursuits, Dr. Allwood’s impact was deeply personal, touching the lives of students, colleagues, and friends alike. Professor Daryl Wout, Chair of the Psychology Department and Associate Professor of Psychology, emphasized her brilliance and passion to spearhead efforts to cultivate a more inclusive environment within our College and at the CUNY university level.
“Dr. Allwood was a beloved member of the John Jay community. She was an active department member and contributed to our students’ development and our clinical program’s growth. She fiercely advocated for an increased focus on diversity, equity, and inclusion (DEI) and spearheaded various DEI efforts at the college and university levels. Her research on the developmental effects of trauma and violence and their disproportionate impacts on different sociodemographic groups has significantly impacted our understanding of this important area. As a mentor, she was extremely supportive and nurturing of her students. She always prioritized her students and their success, even while on sabbatical. Beyond her impact at the College, she was a loyal friend, an exceptional mother, and a committed wife. As a community, we have been blessed by her presence and are deeply mourning her sudden death. She will forever be in our hearts and minds.” said Daryl Wout.
Reflecting on Dr. Allwood’s profound influence, Distinguished Professor Kevin Nadal wrote in his Instagram post, “She was a no-nonsense educator and mentor—someone who wanted her students to succeed while always encouraging them to work their hardest and never make excuses. She was an extraordinary colleague—one of the few humans who made an oppressive place like academia feel welcoming. SHE is what a professor looks like.”
Dr. Maureen Allwood received the 2023 OAR Scholarly Excellence Award winner, exemplifying a commitment to excellence, and has won several accolades and grants for the College. Her most recent groundbreaking study, “Youth Exposure to Gun, Knife, and Physical Assaults,” which examined PTSD symptoms across various demographic groups, was notably featured in Impact Magazine 2023 of the John Jay College of Criminal Justice. Her legacy, as showcased in Impact Magazine, serves as a testament to her enduring influence in shaping our understanding of critical societal issues.
As we honor Dr. Maureen Allwood’s memory, let us carry forward her excellence, compassion, and advocacy legacy. Though she may no longer be with us, her spirit will continue to inspire us to strive for a more just and equitable world.
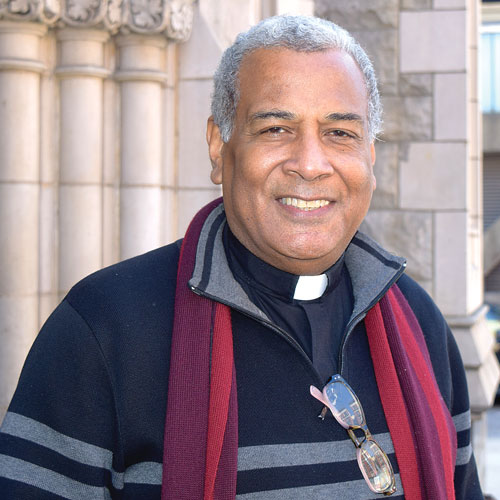
John Jay Institute Director Champions Education, Advocacy, and Policy Change for Black Empowerment

In celebration of Black History Month 2024, Andre Ward, the Executive Director of the John Jay Institute for Justice and Opportunity, reflects on a journey shaped by personal experiences within the criminal legal system. From incarceration to becoming the John Jay Research Center Director, his experiences drive a vision to empower formerly incarcerated individuals through education and to influence policy changes addressing social and racial inequalities. Read more about his background in the Q&A below.
As we celebrate Black History Month, can you share a bit about the journey that led you to John Jay’s Institute for Justice and Opportunity and a professional achievement that you believe has contributed to advancing justice and opportunity for the Black community?
I came to the institute as a result of my past involvement with College Initiative in 2009. I was released from incarceration on January 16, 2009 (the day Martin Luther King Jr’s birthday was observed), and two weeks later, I enrolled in Medgar Evers College. Earning both undergraduate and graduate degrees from CUNY’s Medgar Evers and Herbert H. Lehman Colleges, respectively, created opportunities for me to deepen my commitment to empowering the Black Community. After earning my Master’s Degree in Social Work, I was asked by the department chair at Medgar Evers College to return as an adjunct lecturer, where I taught mostly Black (and Latinx) students for 4 ½ years. Following this professional achievement, I localized myself in non-profit reentry/policy/advocacy work, culminating in a major New York City legislative win with the passage of the Fair Chance for Housing Act in December 2023. This legislation would prevent people with a conviction record from being discriminated against when applying for housing. For many justice-impacted college students like those whom we serve at the Institute for Justice and Opportunity, housing is indispensable to creating stability. This important legislation would protect them and the other 750,000 New Yorkers (80% of whom are Black and Latinx) from being denied access to housing solely on the basis of past justice system involvement.
How has your previous experience prepared you for the role of Research Center Director at the Institute for Justice and Opportunity?
Being directly impacted by the criminal legal system and working with diverse groups and students who had and did not have justice system involvement has prepared me for the role of Research Center Director at the Justice and Opportunity Institute. Additionally, my training as a social worker, policy/legislative change agent, and advocate for justice, fairness, and equity in education, employment, and housing – especially for people with conviction records – has also prepared me for this role. Serving in various capacities in New York City non-profit starting with providing job readiness/career coaching to facilitating academic and life skills workshops for students at Baruch College’s SEEK program and overseeing restorative justice/alternatives to incarceration work for young adults ages, serving as director of workforce development and executive leveled roles in advocacy and education and employment services, has prepared me for this role. My experience of being incarcerated has also served to prepare me for this role.
What is your vision for the Institute in promoting justice and opportunity, particularly within the context of Black communities?
My vision is to expand how we equip formerly incarcerated students with the knowledge and skills necessary for securing gainful employment, an essential factor often impeded by the stigma of a criminal record. Deepening existing stakeholder relationships while simultaneously innovating in areas of program service provision is part of my vision to move toward national and international education efforts.
Given the current social and racial inequalities landscape, how do you see the institute’s role in influencing policy changes that address these disparities?
The institute can support advocacy efforts that address discrimination in education. It can also join voting rights efforts to get our students involved in changing policy/legislation that impacts their lives. Through narrative sharing and engaging elected officials in the city and state, IJO’s students can become empowered to organize their communities to facilitate change. By doing so, members of the community become co-creators of public safety, thus creating the world they want to see and be in.
How do you see the institute actively contributing to the ongoing narrative of Black history and progress?
Education transcends the mere acquisition of knowledge; it serves as a catalyst for personal transformation. For formerly incarcerated individuals, this transformation can be profound. Education instills self-worth, purpose, and a vision for the future, offering a beacon of hope and a pathway to self-improvement. IJO will continue to serve as a place where justice-involved students can come. And through the impact IJO has on students, coupled with students developing an understanding of themselves, they will become assets to the community, creating a history of contribution that adds value to the black community and humanity.
IJO will actively nurture essential life skills, including critical thinking, problem-solving, and decision-making, which can be a powerful tool for psychological healing, helping individuals overcome the stigma and emotional burdens associated with their criminal history.
Western and Redburn (2017) emphasize in their seminal work, Education as Crime Prevention: The Case for Reinvesting in Prison Higher Education, that the role of education is to serve as a platform for self-improvement and a means for shifting individuals’ perspective from their past to their potential. This transformational aspect of education is pivotal in successfully reintegrating formerly incarcerated individuals into society, and IJO will maintain this work – especially during Black History Month.
How are you celebrating Black History Month?
I am celebrating Black History Month by actively making monetary and skills contributions to small Black organizations that support the communities we come from and focus on reentry and higher education services for people with a conviction record. I am also celebrating the amazing good fortune I have to serve our students alongside my deeply committed colleagues at IJO. Together, we are making a difference in the lives of Black people in particular, and humanity generally – one powerful academic student at a time.
Read more about the John Jay Institute for Justice and Opportunity here.
How Black Writers Sought Justice During the Jim Crow Era

In American media history, the Saturday Evening Post, often celebrated for its nostalgic portrayal of American life, undergoes a critical analysis in the groundbreaking book “Circulating Jim Crow: The Saturday Evening Post and the War Against Black Modernity” by Dr. Adam McKible, associate professor of English at John Jay College. This study challenges the idealized image of the iconic publication, exposing its deep connections to racist ideologies during the Jim Crow era, contrary to the widely held belief that the magazine offered an uncomplicated reflection of American life.
The book begins with Dr. McKible exploring the career of George Horace Lorimer, an editor who propelled the Saturday Evening Post to prominence during the modernist era and established the magazine’s remarkable influence. With a readership in the millions, the magazine played a pivotal role in shaping public opinion and influencing households across the nation. Under Lorimer’s editorship, the magazine fueled anti-immigration sentiments by promoting nativist politics and racial pseudoscience, contributing to policies that closed the nation’s borders to immigrants from diverse regions, including southern and eastern Europe, Africa, Asia, and the Caribbean.
“The magazine under Lorimer was very involved in ginning up anti-immigrant sentiment in America and making Americans suspicious of other Americans based on their racial origin,” said Dr. Mckible in an interview with John Jay Research.
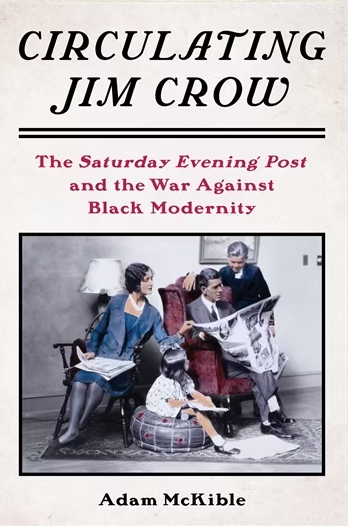 Focusing on the Harlem Renaissance, Dr. McKible’s research also exposes how the Saturday Evening Post portrayed African Americans and responded to changes in Black American life during the Harlem Renaissance. He unveils the magazine’s subtle but insidious approach to addressing the era’s transformations, coining the phrase “register and re-contain” to describe how the magazine acknowledged black achievements only to undermine them through racist stereotyping.
Focusing on the Harlem Renaissance, Dr. McKible’s research also exposes how the Saturday Evening Post portrayed African Americans and responded to changes in Black American life during the Harlem Renaissance. He unveils the magazine’s subtle but insidious approach to addressing the era’s transformations, coining the phrase “register and re-contain” to describe how the magazine acknowledged black achievements only to undermine them through racist stereotyping.
Dr. McKible’s findings reveal that despite recognizing the emergence of black modernity, the magazine consistently endeavored to restrain and belittle black accomplishments, transforming them into subjects of ridicule or disregard. This dismissive approach extended to influential figures such as Booker T. Washington and other black leaders during the Harlem Renaissance, as the Saturday Evening Post downplayed their contributions.
In response, black writers resisted the magazine’s narratives by taking aim at the white writers who were widely recognized as Saturday Evening Post authors. By naming such figures, as famous Post authors as Octavus Roy Cohen and Irvin S. Cobb, Harlem Renaissance writers signaled their displeasure with and resistance to the caricatures and stereotypes perpetuated by Lorimer’s magazine.
“With the help of the Saturday Evening Post, America took on the work of establishing Jim Crow, legally and culturally. These were not legal efforts but instead cultural maneuvers designed to denigrate, demean and dismiss black humanity, to take back everything that happened during Reconstruction and destroy it,” says Dr. Mckible in an interview.
Expanding the history to contemporary implications, Dr. McKible emphasizes the importance of truth-telling, challenging nostalgia, recognizing that America’s history is fraught with complexities, and acknowledging the deep-rooted racial inequalities that persist.
“The contemporary media should always tell the truth,” Dr. Mckible emphasizes.
Dr. McKible’s groundbreaking research redefines our understanding of the Saturday Evening Post and contributes to contemporary discussions about media responsibility, representation, and the ongoing struggle for racial equality.
Read about Dr. McKible’s Research here.
New Faculty Spotlight Interview: Prof. Alessandra Early

Professor Alessandra Early is an assistant professor of Criminal Justice at John Jay College and a dedicated criminologist whose academic journey is rooted in a passion for understanding the intricacies of human behavior and identity. From a childhood curiosity that questioned the fundamental nature of numbers to becoming a professor, her commitment to knowledge has been unwavering. With a background in psychology and sociology, she transitioned to criminology, driven by a fascination with the dynamics explored in shows like Criminal Minds.
Dr. Early’s research delves into the intersection of spatial dynamics, identity formation, and behavior, particularly focusing on queer experiences and the impact of social spaces. In this Q&A, Dr. Early shares her insights into research, professional achievements, mentoring philosophy, and her vision for contributing to the academic community.
Can you share a bit about your academic journey and what led you to pursue a career in criminology?
Since I was young, I’ve wanted to help people and investigate the “hows” and “whys” behind everything around me. As a kid learning math, I peppered my mother with questions incessantly, completely unsatisfied with the superficial and desperately seeking to learn a greater meaning. “Why is a one a one?” I asked. “What makes a two a two?” That pursuit of knowledge has become a core mission in my life and led me to become a professor today.
As an undergrad, I majored in psychology and sociology. I fantasized about becoming an FBI profiler thanks to my obsession with Criminal Minds, and I kept finding myself drawn to criminology courses. That tendency persisted when I pursued my master’s in sociology as well; I really connected with some professors who really believed in me and my work. I decided to follow that path and complete my PhD in criminology and criminal justice. (Though I moved away from law enforcement.)
Being a professor means I always have to adapt and evolve as new knowledge develops, which I love. I enjoy reading, learning, and problem-solving and my job asks me to engage in all three. Interacting with students is such a privilege because I want them to have the same light-bulb “Aha!” moments in my classrooms that I used to experience as a student myself.
Could you highlight some of your key research interests or projects, and how do you see them contributing to your field or broader society?
Broadly speaking, my research is rooted in three intersecting areas: Spatial and place-based dynamics, identity formation, and behavior. Specifically, I am interested in the ways in which spaces, particularly social spaces, impact how people understand themselves and can encourage or inhibit behavior. My dissertation, for example, explored how the historical, social, and cultural spatial dynamics of queer social spaces (such as bars and clubs), and using substances within them, can impact queer identities. One finding was that queer people strategically used substances to explore their identities and navigate queer vs. heterosexual social spaces.
Another project investigated the interplay between space(s), identities, and substance use through the experiences of primarily white heterosexual women who had experience with the rural methamphetamine market before being incarcerated. We emphasized the complex, violent, and empowering strategies that women used to confront and overcome gendered and sexualized expectations while participating within the patriarchal market.
My research interests engage in “queering” or destabilizing normative understandings of how we move through our environments, create meaning within them, formulate our identities in opposition to or with the help of those environments, and how those environments and the meanings we prescribe to them encourage or inhibit our behaviors.
Have there been any significant milestones or achievements in your professional journey that you are particularly proud of?
Currently, I’m most proud of my paper, The Role of Sex and Compulsory Heterosexuality Within the Rural Methamphetamine Market, which was published in Crime & Delinquency. Because of the precarious nature of grad school, sometimes it’s hard to see a project from inception to completion. To my and my co-author’s knowledge, this article represents the first paper to apply a queer criminological framework to examine the experiences of primarily cisgender and heterosexual white women. In 2022, the paper earned first place in the inaugural student paper award from the Division of Queer Criminology at the American Society of Criminology.
Do you have a mentoring philosophy, and how do you envision supporting students in their academic and professional development?
I approach teaching as a way to co-construct knowledge with students, with the goal of transforming the classroom into an encouraging space and making the material relatable and accessible. My mentoring philosophy builds upon that same foundation, emphasizing a collaborative and comfortable environment that I strive to offer all my mentees. I often describe my personal experiences with employing particular methodologies, concepts, or theories in order to demystify learning and the process of conducting research. In one-on-one student conversations and larger panel events, I speak candidly and transparently about the joys and challenges of being a Black queer woman in academia. While at conferences, I carve out time to bond with my mentees and ensure that I introduce them to fellow academics who share their interests to encourage networking and professional advancement. I let them know that my door is always open.
How do you envision contributing to the growth and development of our academic community in the coming years?
Although I have only spent a few months here at John Jay, I’m currently working to develop new courses that consider the ways in which queerness intersects with the carceral system and deepen our understanding of qualitative methodologies. I also look forward to carving out pathways that combine critical analyses and intersectional education.
Outside of academia, what are some of your hobbies or interests?
Outside of academia, you can find me practicing Matsubayashi Shorin-Ryu karate and Matayoshi Kobudo (traditional weapons). Currently, I am a Shodan (1st-degree black belt) and I am preparing for my Nidan (2nd-degree black belt) test in the fall of 2024! I’ve also recently rekindled my love for video games (after a long hiatus during graduate school) and I’m back to gaming with my friends!
If you could give one piece of advice to students aspiring to excel in your field, what would it be?
Throughout my educational career, I have always carried my grandmother’s mantra and work ethic, which is the best advice I’ve ever received: Good, better, best. Never let it rest until the good is better and the better is the best. Though I’d make one small amendment — rest is important! Be sure to take breaks, but keep those intellectual fires burning.
Q&A With Dr. Suvi Rautio, 2023 John Jay Research Visiting Fellow
In our Q&A series, the Office for the Advancement of Research (OAR) is excited to spotlight the 2023 Visiting Research Fellow, Dr. Suvi Rautio for the vital research she has conducted. Suvi is an anthropologist specializing in urbanization and transnationalism in rural China. Guided by family history stories, she delivered a public lecture to the John Jay College Community on April 4, 2023, titled: The Love Letters: Dreams at the Dawn of the Mao Zedong Era.
In this Q&A, Suvi shares her experience as a Visiting Fellow at John Jay College, discusses the research projects she’s worked on, and offers academic advice.
Tell us about your career path?
I started my career path in Beijing, China, working on a large range of different jobs, most of which were completely disconnected from academia and anthropology. Having grown up in Beijing, I had always been concerned in the impact that China’s breakneck development was having on the environment. I grew increasingly curious in the experience of environmental loss – in particular, how this loss alters people’s sense of belonging. This curiosity led me to work for Greenpeace where I led a research team to understand what forms of messaging and campaign strategies resonates with the broader Chinese audience. This felt exciting and meaningful, but it also did not feel like I was doing enough. I was seeking answers to bigger questions. Eventually I understood that I needed to return to academia to attend to my curiosity.
When I started a PhD in anthropology, my research in Southwest China steered me away from questions on the environment to cultural heritage. Although I was no longer focusing on environmental change, my interests in place-making and belonging have remained central to my research. To this day, my anthropological analysis pursues to find answers to how people’s connections to place and belonging change when they experience a sense of loss in one form or another.
What shaped you on your journey to follow your family’s history?
I always knew I wanted to do research on my family history. Growing up in Beijing, I wanted to understand what my family members experienced during the Maoist era — a time in which China was a very different country from the one I was familiar with. My family members did not share or openly speak about stories of the past spoken. Something inside of me has always wanted to understand and peel the layers of my family’s silences.
Maybe a part of this drive was to understand my father’s story growing up in Beijing, which I thought might help me make sense of some of the feelings that I was experiencing living in Beijing. I have always been a bit torn by the experience of feeling a deep association towards a city that I spent most of my childhood and early adulthood but where I am at the same time treated and seen as a foreigner and thus an outcast of the wider Chinese public society. Maybe if I can understand how these processes have been experienced through the lives of my family members, I can also find explanations for my own.
At the beginning, I was unaware that studying my family history was something that I could do as an anthropologist. I thought a study on my own history would appear too self-centered, and of little interest to outsiders. It was only when I was exposed to Alisse Waterston’s work (through Paul Stoller) did I learn that this is not the case. Alisse’s work has been and continues to be fundamental in shaping my journey conducting an intimate ethnography on my family.
My previous research was also fundamental in paving the path to studying my family history. Before my PhD research, I would not have been ready to pursue research on my family history. Academia is structured around critical thinking and critique, and I was scared of having to face that critique on something that is so personal. I was not ready to attend to that. Little did I know that my PhD would also become very personal, and in my dissertation I was very honest about the intimate relationships I formed with my interlocutors. This intimacy has been faced with critique. Rather than silencing those intimacies, writing about them has helped me gain a level of professionalism and courage as a writer and anthropologist. Most importantly, as an anthropologist, I have grown to understand that my research projects tends to get very personal very fast. I now understand that rather than fearing that feeling of intimacy, it is something I need to come to terms with.
Why did you want to share your story with the John Jay Community?
It was such an honour to be invited to share my work at a college-wide lecture with the John Jay Community. I wanted to take the opportunity to share my story and to challenge myself by presenting some initial material I have been collecting on my project. Sharing my story in front of my students and peers felt meaningful and I am very appreciative of the opportunity that was offered to me.
Based on the love letters you shared with us, what does love mean to you?
Love is about offering our thoughtful attention and care to someone or something. The stories that unfold in the love letters has taught me that. I think this quote, which I mention in my talk written by Armi, my grandmother, in her letter to my grandfather epitomizes how unrestrained love should be:
“Love is about whether we can understand and appreciate each other, and whether we are able to speak the same language of heart. And if we don’t understand each other in the beginning, we must be able to show that we can give the other an opportunity for mental liberty and give up our own ideas if we feel we are wronged.”
How does the love letter lecture at John Jay differ from other events you discussed?
I often present my work at conference panels and am more familiar with presenting my work within the time constraints of 10 to 20 minutes. Presenting at John Jay offered a rare opportunity to share my work beyond these time constraints. I also really appreciated having time for questions from the audience. For me, it’s these moments hearing about how my research engages with others that makes academic events, such as the one that John Jay offered me, so meaningful and worthwhile.
Overall I was really impressed by how well organized the lecture at John Jay was – from the preparation of the food and drinks, to the marketing and promotion, and all the other backend work that Remmy Bahati worked hard to put together. I was also impressed that the college had organized a professional video producer to film the lecture. Justin Thomas, the producer did a great job at this.
How did the speech make you feel?
I was so nervous about my presentation before the event. When it was over, a wave of relief swept over me when the audience showed so much enthusiasm and support towards my project. It was also moving to hear how my presentation resonated with audience members. This gave me a big boost of energy to continue moving forward with my project. Overall, the event gave me confidence to continue to seek opportunities to discuss and share my work.
Is there anything else you would like to share?
Thank you John Jay for this opportunity to share my work!
Back to the Lab with Dr. Jason Rauceo

John Jay College, along with CUNY schools across the city, are moving toward the resumption of on-campus life. Classes are attended in-person, events are being planned, and professors and students alike are headed back into the laboratory. I talked to one of John Jay’s professors in the Department of Sciences, Dr. Jason Rauceo, to find out what it’s been like closing down and reopening his lab.
Dr. Rauceo is an Associate Professor of Biology whose research focuses on the major fungal pathogen Candida albicans. He is also the Director of the Cell and Molecular Biology major at John Jay. In 2021, Dr. Rauceo received a four-year grant from the National Institutes of Health to study the role of the mitochondrion in C. albicans’ ability to infect hosts and cause disease.
What was it like to get back to lab work after a significant time away during the early part of the pandemic? Did you have to change any protocols or make adjustments to your operating procedures?
Right before CUNY closed in March 2020, I shut the lab down with the expectation that I would not return for 6-12 months. I returned to campus in September 2020, and the major challenge was reopening the lab myself. Students were not allowed on campus, and I needed to calibrate several instruments that I had limited experience operating. Fortunately, my students were available via Zoom and FaceTime for assistance.
What does a typical day in the lab look like, if there is such a thing?
The day usually begins with a short one-to-one meeting with whomever is scheduled to perform an experiment, in which we mainly discuss logistics. Throughout the day, I periodically check in to assist and address any experimental issues if needed. At the end of the day, I inspect the lab to make sure that workspaces are cleaned, all reagents and supplies are properly stored, and all students have left the lab.
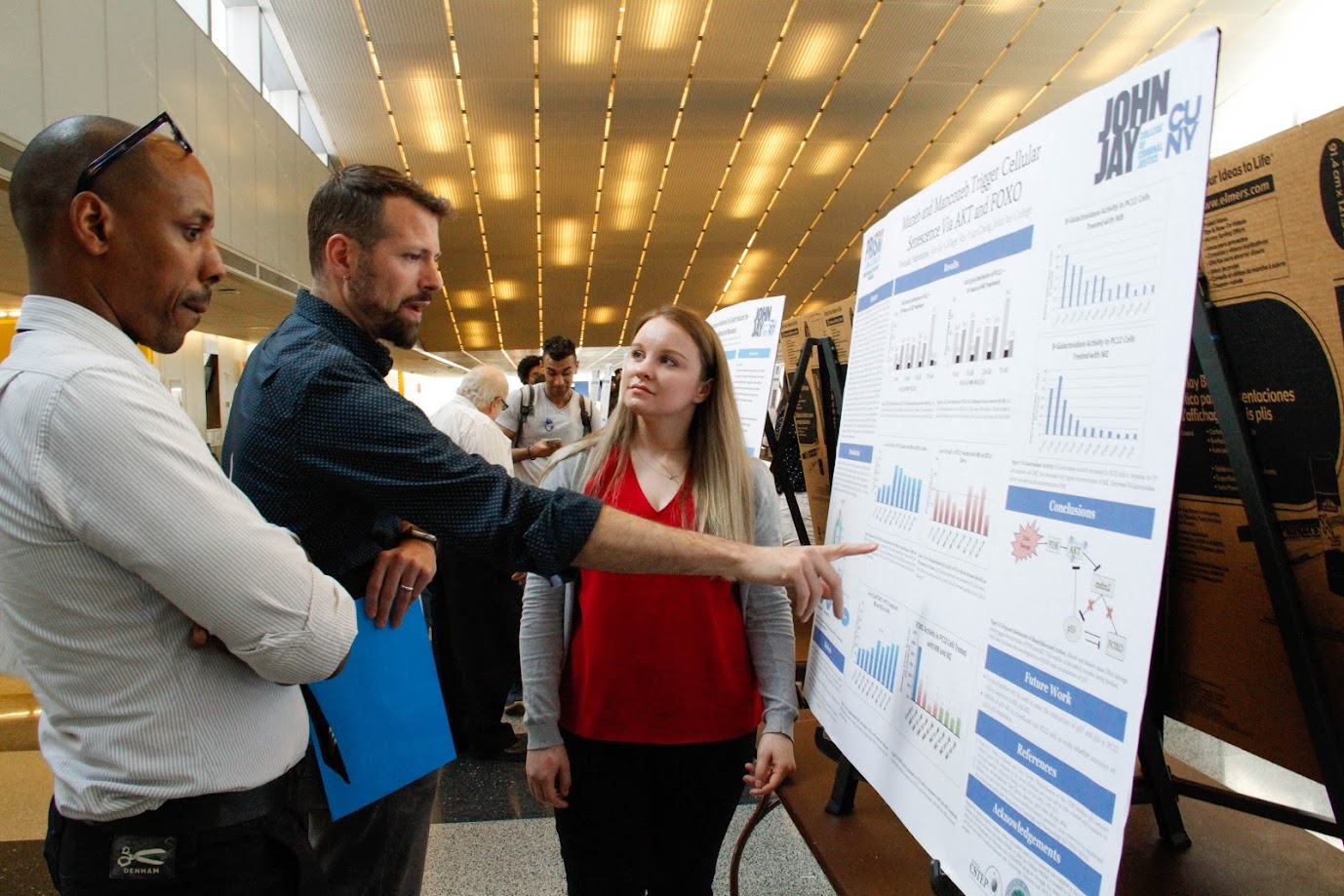
What function do students play in your lab?
Students perform the hands-on experimentation and data analysis, and are responsible for general lab maintenance. They also contribute to the development of their projects, which must be directly related to the lab agenda—in this case, C. albicans biology. Students may propose their own experiments for approval after approximately 1.5 to 2 years of experience in the lab.
You place a lot of emphasis on experiential-based learning. What does that mean in practice for your students?
I allow students to test their own hypotheses when safety and costs are not an issue. Also, I allow students to make their own errors during initial training exercises. I found that this approach in lab research builds confidence.
Generally, in the early stages of a new project, a significant amount of time is devoted to optimizing protocols to meet our objectives. During this “optimization phase” of the research, there is an extensive level of troubleshooting required, and a high level of error and ambiguity is observed. I found that a major payoff of experiential-based learning and training is that students propose unique approaches to addressing experimental obstacles.
Your study of SPFH (Stomatin, Prohibitin, Flotillin, HflK/HflC) proteins’ role in mitochondrial function in Candida albicans is being funded by the NIH. It seems that there are some exciting implications for developing antifungal treatments—can you tell me about that?
SPFH proteins are widely conserved in nature and are found in most living organisms. These proteins are important for major biological processes including, but not limited to, respiration, transport, and communication. Candida albicans is a fungus that resides in all humans on mucosal surfaces such as the mouth and gastrointestinal tract in a harmless state. However, changes in our immunity sometimes cause C. albicans infections. Immunocompromised individuals are highly susceptible to C. albicans infections.
Currently, the function of SPFH proteins is limited in C. albicans. We were the first research group to demonstrate that SPFH proteins are required when C. albicans is challenged with environmental stress. Our current proposal seeks to define the molecular function of SPFH proteins. We are collaborating with several prominent research groups in fungal biology and medicinal chemistry to determine the function of the SPFH proteins in mitochondrial function.
One of our project aims is to understand the effects of treating C. albicans with natural compounds that target SPFH proteins. Our initial findings are promising and may be useful in developing novel antifungal strategies.
The NIH award provided me with the funds to expand my lab operations, and I’ve recruited three new undergraduate students; therefore, I will be spending much of the next semester in student training and performing experiments.
Sewage and the Science of Public Health – Dr. Shu-Yuan Cheng and Dr. Marta Concheiro-Guisan Track Wastewater Contaminants

Wastewater is a topic that the average New Yorker doesn’t think about often, but perhaps we should. Sewage and run-off, over a billion gallons of which are treated every single day in New York City by 14 wastewater resource recovery facilities, are a valuable resource for scientists.
Wastewater sampling has been a useful tool for public health researchers tracking the COVID-19 pandemic over the last two years. The Centers for Disease Control (CDC) launched the National Wastewater Surveillance System in September 2020 as a means of tracking virus spread and community prevalence. Viral genetic material is transmitted in fecal matter to the sewers and waste treatment plants, where researchers can take samples. Their work can serve as an early warning of community spread, track variants, and inform public health strategies for responding to the virus. Even better, wastewater surveillance doesn’t require individuals to seek out healthcare in order to capture information, meaning that the resulting data can include people who may be asymptomatic, who have taken home tests, or who have not been tested at all.
Wastewater data have figured prominently in several interesting COVID-19 stories recently in the news. In January 2022 the CDC reported that mutations associated with the Omicron variant showed up in New York City wastewater in November 2021, before the variant was officially reported in South Africa and at least a week before the first U.S. case was identified via clinical testing, suggesting that Omicron was likely circulating in communities before cases could be officially confirmed. And The New York Times recently reported on mysterious fragments of viral RNA with novel mutations detected in NYC wastewater, which are stumping researchers. They haven’t been able to pin down where these fragments are coming from, nor why these mutations have not shown up in clinical testing of human or animal populations in the city.

Two John Jay College researchers, Dr. Shu-Yuan Cheng and Dr. Marta Concheiro-Guisan, are also big proponents of wastewater sampling studies as a public health tool. Their own research, published in 2019, tracked drug use over one year in New York City, using one-time grab samples to test for levels of cocaine, nicotine, cannabis, opioids, and amphetamines in the sewage. Now, the scientists are collaborating with non-profits that test the health of the city’s waterways, trying to correlate levels of pharmaceuticals in our rivers with the amount of harmful bacteria.
To Dr. Cheng and Dr. Concheiro-Guisan, wastewater analysis’s great strength lies in early warning and early intervention. “It’s a great tool for prediction, for public health, crime fighting, and disease [prevention] purposes,” says Dr. Cheng. “The official report is often too late, but if you can do an early intervention, find the issue and start addressing it, there’s a lot you can do.”
“We looked at wastewater because we saw the utility,” says Dr. Concheiro-Guisan. “This is a different application [than viral tracking] but with the same thought: that what we eliminate from our bodies tells you a lot about your population.”
However, the United States is late to the game. Though the CDC has had results with its national COVID-19 tracking program, both researchers lament the lack of a centralized American body to apply this research to other public health applications. They’d like to see the U.S. follow the example set in European countries, China, Australia, and increasingly in South America, where governments have applied wastewater sampling to create campaigns warning their citizens about novel psychoactives, catch drug manufacturers, and more.
“It’s a very important public health tool that is showing results,” says Dr. Concheiro-Guisan. “If you start in the biggest city in the country, if you start in New York, then others will follow.”
 Dr. Shu-Yuan Cheng is an Associate Professor and Chair of John Jay’s Department of Sciences. Her research is in the areas of toxicology and forensic pharmacology, including the roles that environmental toxins play in neurodegenerative diseases, identifying the target genes and signaling pathways affected by environmental toxins, and investigating pharmacological mechanisms of anti-cancer medications.
Dr. Shu-Yuan Cheng is an Associate Professor and Chair of John Jay’s Department of Sciences. Her research is in the areas of toxicology and forensic pharmacology, including the roles that environmental toxins play in neurodegenerative diseases, identifying the target genes and signaling pathways affected by environmental toxins, and investigating pharmacological mechanisms of anti-cancer medications.
 Dr. Marta Concheiro-Guisan is Assistant Professor of Forensic Toxicology in John Jay’s Department of Sciences. Her research focuses on the development and validation of analytical methods by gas and liquid chromatography tandem mass spectrometry and their application to different specimens, the detection of drug exposure during pregnancy, and the toxicological study of new psychoactive substances.
Dr. Marta Concheiro-Guisan is Assistant Professor of Forensic Toxicology in John Jay’s Department of Sciences. Her research focuses on the development and validation of analytical methods by gas and liquid chromatography tandem mass spectrometry and their application to different specimens, the detection of drug exposure during pregnancy, and the toxicological study of new psychoactive substances.
Critical Sociology At Work Around the Globe – David Brotherton and the Social Change Project
Dr. David Brotherton is in high demand. As founder and director of the Social Change and Transgressive Studies Project, a research project at John Jay, he leads grants that span multiple countries and touch subjects from post-release reintegration to immigration and the deportation pipeline. His long background and expertise in critical criminology and sociology have suited him to lead the varied types of prestigious grants the project obtains. Brotherton says that the work has three key points of overlap: “One part is to be able to transcend the academy, to translate your findings from the theory to what it actually means to people. Second, you’re doing work that immediately has an impact, to understand or respond to a social problem. And the third thing is to work with the underrepresented, the marginalized, and to help develop knowledge that goes back to them, to empower them.”
With a mission statement like that, how could the Social Change Project not have ended up at John Jay College? Founded in 2017, the organization almost lived at the CUNY Graduate Center; however, a set of happy accidents brought it to John Jay, where, co-directed by Brotherton and Professor of Sociology Dr. Jayne Mooney, it has been funded every year. Under the project’s umbrella live two working groups: the Social Anatomy of a Deportation Regime, a working group that focuses on “crimmigration” and the dynamics of border control and migrant detention, and the Critical Social History Project, which features Mooney’s work chronicling the history of incarceration in New York. Today, the Social Change Project is doing work with ramifications that will be felt all over the globe.
The Deportation Pipeline
 Growing up in a working class London neighborhood, Brotherton has always been interested in the day-to-day conditions and labelling faced by people just trying to get by. His first career in youth organizing and present career in sociology and criminology have a focus in common: applying knowledge to empower the disadvantaged. His background led him to research gangs and incarceration, which brought him to the place he is in today.
Growing up in a working class London neighborhood, Brotherton has always been interested in the day-to-day conditions and labelling faced by people just trying to get by. His first career in youth organizing and present career in sociology and criminology have a focus in common: applying knowledge to empower the disadvantaged. His background led him to research gangs and incarceration, which brought him to the place he is in today.
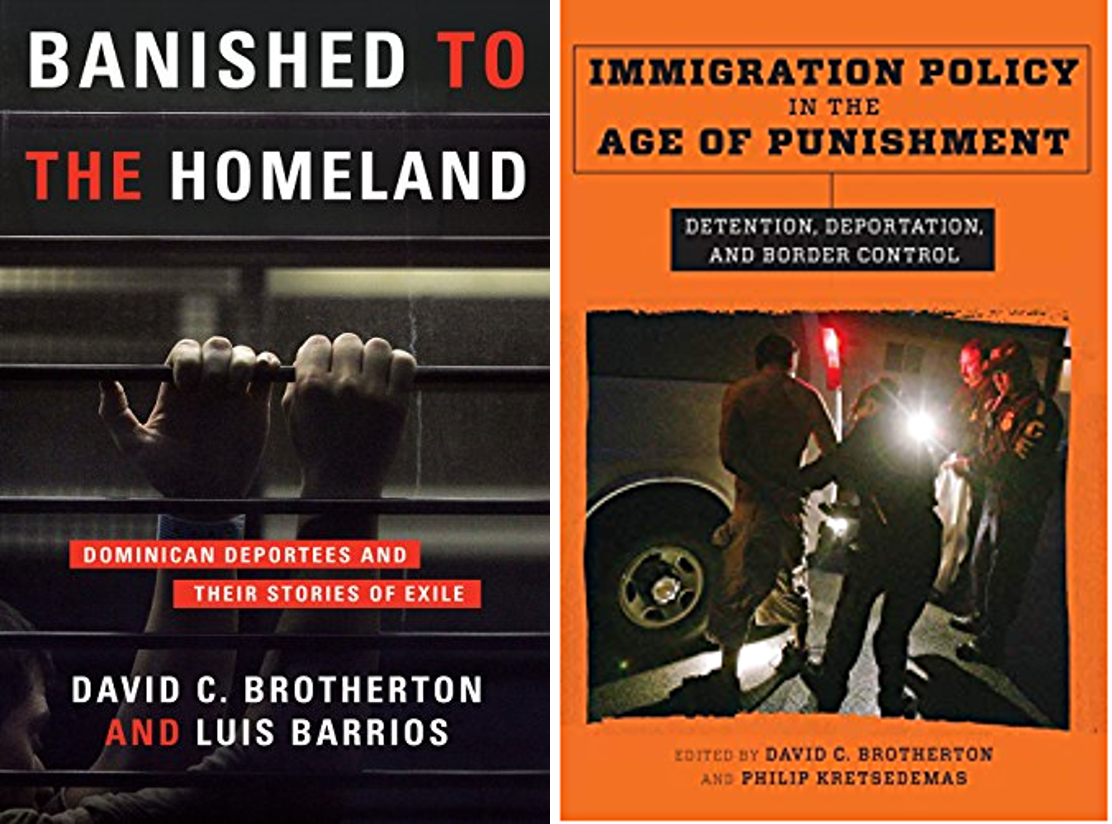
As he tells the story, Brotherton’s work with infamous gang organization the Latin Kings in New York brought him to the Dominican Republic in the early 2000s, where he was giving a talk on his project. “People didn’t want to know about the gangs, all they wanted to know was, why are you sending them all back here?” says Brotherton. “And I said, ‘I don’t know, but I’ll find out.’” That was the start of his investigations into transnational gangs and the issue of deportation, which at the time was not well-studied. That work has led to multiple grants and studies, books including Banished to the Homeland: Dominican Deportees and Their Stories of Exile and Immigration Policy in the Age of Punishment: Detention, Deportation, Border Control, and the evolution of the multinational TRANSGANG project in Europe, which he advises.
This spring, Brotherton’s project will be working with personnel from Rutgers, including John Jay College graduate Sarah Tosh, to kick off the Deportation Pipeline Project, funded by the National Science Foundation. The team will interview a variety of subjects – immigrants from the Dominican Republic, Jamaica, and Trinidad and Tobago, including some who have been detained for deportation hearings; lawyers; judges; and even ICE agents if possible – to understand the racialized “deportation pipeline” that runs through NYC back to the Caribbean, and the current situation these communities are living through under the Biden Administration.
“We need to understand all this, and then we’re going to be looking at all the texts that come down, the sanctions, all the laws. We know that Biden has said we’re going after criminal agents and gang members, which is just carrying on from Trump, but I thought we were supposed to have a new, more humane approach. So is it new wine in old bottles or are we going to get a real change in behavior? I don’t know.”
The two-year study will culminate in a book on the topic, as well as a conference with representatives from other municipalities. But Brotherton is already looking past the conclusion of the research to a potential comparative study in another large city or small town, to understand the dynamics of deportation in other American environments with similar demographics being targeted by immigration officials.
Critical Gang Studies
The Social Change Project is also looking forward to wrapping up several projects in the coming months. Since 2019, Brotherton has been consulting for the World Bank in El Salvador, developing national strategies for rehabilitation and reinsertion programs for formerly-incarcerated gang members in that country, which has the second-highest rate of imprisonment in the world after the United States. In April the project published a paper summarizing those findings, and expanding on them. “As we were writing this, we realized there is no real program for rehabilitation anywhere in Latin America, no probation, nothing like that,” says Brotherton. “Once you come out of prison, you’re on your own. So what we’re developing for El Salvador is really a model for the whole of Latin America.”
And July will see the publication of an edited volume, the Routledge International Handbook of Critical Gang Studies, which Brotherton edited along with Rafael Jose Gude, a Research Fellow at the Social Change Project. The book, which includes chapters by a number of CUNY faculty and graduates, will offer new perspectives on gang studies, placing them in the context of their political and social environments. According to Brotherton, it will cover perhaps 18 different countries and will be the largest handbook Routledge has ever released at nearly 900 pages long.
Incarceration and the Credible Messengers
Finally, Brotherton is working on a book on the Credible Messenger phenomenon, due out in 2022. The book, titled What’s Love Got To Do With It?: Credible Messengers and the Power of Transformative Mentoring, begins with a history of the now-widespread program, which recruits the formerly-incarcerated to intervene with young, at-risk kids from their neighborhoods, to keep them away from involvement with the criminal legal system. The book also incorporates qualitative research, including interviews with Messengers, kids, and administrators, as well as the currently incarcerated.
The Social Change Project and Brotherton himself are juggling many projects, each with many moving parts. But Brotherton relies on the connections he’s made over his career teaching at both John Jay and the CUNY Graduate Center, and doing research around the world, to keep the plates spinning. “It’s difficult,” he says. “Sometimes it gets overwhelming, but I always try to make sure I’ve got really good people in each project.”
At the end of the day, Brotherton is proud to be doing work that makes a difference for underserved, understudied communities that can face immense challenges. “I think the project carries on a rich tradition at John Jay. We’re following that tradition of socially conscious, critical social science.”
 Dr. David Brotherton is a Professor of Sociology at John Jay College, and of Urban Education at the CUNY Graduate Center. His research focuses on gangs and globalization, immigration, and deportation and border control. He is the author of numerous books and articles, and has received grants from a variety of public and private agencies.
Dr. David Brotherton is a Professor of Sociology at John Jay College, and of Urban Education at the CUNY Graduate Center. His research focuses on gangs and globalization, immigration, and deportation and border control. He is the author of numerous books and articles, and has received grants from a variety of public and private agencies.
Frank Pezzella Wants Increased Accountability on Hate Crime Reporting
During the chaotic years of the Trump Administration, the United States experienced a rise in hate crimes. This increase has been confirmed by FBI data collection, media reporting, and independent scholarship. According to Dr. Frank Pezzella, an Associate Professor of Criminal Justice at John Jay College and a scholar of hate crimes, four out of the past five years, from 2015 to 2019, have seen consecutive increases in hate crime offending in this country, something he says is new. Nine of the ten largest American cities had the most dramatic increases in hate crimes – including New York City.
Hate crimes, or bias crimes, are strictly defined by the FBI. The organization sets out 14 indicators that must be present for a criminal offense to be classified as a hate or bias crime, that provide objective evidence that the crime was motivated by bias. But according to Dr. Pezzella, the evidence to meet those criteria isn’t always clear. Not every hate crime is as flagrant as the Pulse nightclub shooting in 2016 or the 2018 attack on Pittsburgh’s Tree of Life Synagogue. To establish a hate crime was committed, first responding police officers must look for evidence of bias motivation – what Pezzella calls an “elevated mens rea” requirement. But bias can only be committed against legally protected categories, like race and ethnicity, sexual or gender orientation, disability, or religion, which vary from state to state. And the additional paperwork and procedural requirements that come with classifying an incident as a hate crime are, in his words, disincentivizing police reporting.
Undercounting Hate Crimes
 The result of these complications is rampant underreporting. In his new book, The Measurement of Hate Crimes in America, Dr. Pezzella looks at the reasons why hate crimes are so undercounted in the United States, and proposes some solutions for what law enforcement and policymakers can do to correct the issue. Since the enactment of the federal Hate Crimes Statistics Act in 1990, which required the Attorney General to collect data about hate crimes, the FBI has been fulfilling this mandate in the form of the Hate Crime Statistics Program, published annually as part of the Uniform Crime Report. According to Dr. Pezzella, since 1990 the UCR has reported an average of roughly 8,000 hate crimes per year; but victims, he says, report around 250,000 hate crimes per year. He attributes this substantial gap to a variety of factors including the evidentiary and procedural barriers noted above. In addition, only about 100,000 of these victimizations are ever reported to the police in the first place. And when victims do report, police departments are under no legal requirement to pass their findings on to the FBI.
The result of these complications is rampant underreporting. In his new book, The Measurement of Hate Crimes in America, Dr. Pezzella looks at the reasons why hate crimes are so undercounted in the United States, and proposes some solutions for what law enforcement and policymakers can do to correct the issue. Since the enactment of the federal Hate Crimes Statistics Act in 1990, which required the Attorney General to collect data about hate crimes, the FBI has been fulfilling this mandate in the form of the Hate Crime Statistics Program, published annually as part of the Uniform Crime Report. According to Dr. Pezzella, since 1990 the UCR has reported an average of roughly 8,000 hate crimes per year; but victims, he says, report around 250,000 hate crimes per year. He attributes this substantial gap to a variety of factors including the evidentiary and procedural barriers noted above. In addition, only about 100,000 of these victimizations are ever reported to the police in the first place. And when victims do report, police departments are under no legal requirement to pass their findings on to the FBI.
“Of the roughly 18,500 police departments, only maybe 75% participate in the Uniform Crime Report hate crime reporting program – note that it is voluntary,” says Pezzella. “So we don’t even know about hate crimes in 25% of precincts. And of the participating 75%, roughly 90% report zero hate crimes every year. So one of the reasons we wrote the book is that, either we don’t have hate crimes the way we think we do, or we have a systemic reporting problem.” It’s obvious which he believes is true.
The consequences of underreporting hate crimes are severe, Dr. Pezzella says. “To the extent that we underreport both the type and extent of victimization, it really does put a specific policy issue in front of us. We need to know who’s being affected, how they’re being affected, and the extent of the effect, in order to fashion remedies.” The only way to target treatment and services for the most vulnerable and likely victims is through accurate reporting.
Remedying Undercounting
In order to remedy undercounting and better target policy, Dr. Pezzella presents a number of recommendations in The Measurement of Hate Crimes in America. He calls for changes to take place within police departments, at the level of state and local politics, and in the criminal legal system. First, he suggests that every precinct have a written and clearly posted hate crime policy, and that every officer be trained to understand the rules for identifying bias crimes and the statutes governing them in their particular state. He would also like to see greater police-community engagement on this issue, with better tracking of non-criminal bias incidents – like seeing a swastika or other racist tag in the neighborhood – which Pezzella says often lead to violent bias crimes. He would especially like to see hate crime reporting made mandatory, with penalties or audits following a departmental report of zero bias crimes in a year.
Stepping out of police departments, Dr. Pezzella also calls for greater engagement from state and local politicians, who after all control the purse strings as well as set state legislation, but who are often hesitant to call attention to a problem with hate crimes in their district. Finally, he wants prosecutors’ offices to commit to seeking hate crime convictions, rather than settling for the easier task of convicting an offender for non-bias equivalents. With every actor across the board invested in tackling hate crimes and being transparent and proactive about applying best practices, offenders are put on notice that the community, including police, won’t allow these harmful crimes to continue.
Vicarious Victimization
Dr. Pezzella has been studying hate crimes since his graduate school years at SUNY-Albany, but he doesn’t feel he’s reached the end of this line of research. Going forward, he is interested in studying the deleterious and vicarious effects hate crimes can have on the victims’ communities. Because bias-motivated offenders target victims based on what they are rather than what they do, Dr. Pezzella says, there is a sense that anyone could become the next victim. This impersonal threat undermines societal ideals of trust and equality, and can even affect property values, as whole groups feel unsafe in certain areas and may be forced to relocate. Pezzella also mentions the psychological and emotional impacts of feeling under threat for simply being who and what you are. “When a victim goes home and says they were a victim of a hate crime, in what way does it impact the quality of life or sense of safety for secondary victims [i.e., the victim’s community]?” he asks. “What do they do? While we understand the direct impact, we know less about this vicarious impact, and how far it extends beyond the primary victim.”
He also has his eye on current events, especially the rise of domestic terrorism in the United States. Dr. Pezzella is concerned about the growing number of organized hate groups in recent years, and how emboldened they have been by rhetoric from the top levels of government. While many mass shootings have been categorized as domestic terrorism, Pezzella also sees evidence of bias that might categorize these events as hate crimes. If they are being left out of crucial counts that help to allocate resources and fight back against hate in this country, he wants to know.
 Dr. Frank Pezzella is an Associate Professor of Criminal Justice at John Jay College. His primary research focus is on the causes, correlates, and consequences of hate crimes victimizations. He also conducts research on issues that relate to race, crime and justice. In addition to his most recent book, he is also the author of Hate Crime Statutes: A Public Policy and Law Enforcement Dilemma, as well as numerous peer-reviewed articles.
Dr. Frank Pezzella is an Associate Professor of Criminal Justice at John Jay College. His primary research focus is on the causes, correlates, and consequences of hate crimes victimizations. He also conducts research on issues that relate to race, crime and justice. In addition to his most recent book, he is also the author of Hate Crime Statutes: A Public Policy and Law Enforcement Dilemma, as well as numerous peer-reviewed articles.

 Dr. Luis Barrios has been a faculty member at John Jay College for 28 years, and at CUNY for even longer. During that time, he has worked on projects that blend social action and scholarship, involving gangs and gang violence, deportation, human rights, clinical work focused on trauma and abuse, and contemporary perspectives of life on the Dominican-Haitian border.
Dr. Luis Barrios has been a faculty member at John Jay College for 28 years, and at CUNY for even longer. During that time, he has worked on projects that blend social action and scholarship, involving gangs and gang violence, deportation, human rights, clinical work focused on trauma and abuse, and contemporary perspectives of life on the Dominican-Haitian border.


Recent Comments